In the fast-evolving landscape of cybersecurity, the emergence of artificial intelligence (AI) has become a game-changer. AI has proven to be a powerful ally in the battle against sophisticated threats, empowering organizations with advanced detection and defense mechanisms. With its ability to analyze vast amounts of data, AI can swiftly identify anomalies and patterns that humans may overlook, making it an invaluable tool in safeguarding sensitive information and preventing cyberattacks. In this article, we will explore how the integration of AI into cybersecurity operations is revolutionizing the way we detect and defend against increasingly complex and insidious threats.
The Role of AI in Cybersecurity
Understanding the Importance of AI in Cybersecurity
In today’s digital age, where cyber threats are becoming increasingly sophisticated and prevalent, the role of artificial intelligence (AI) in cybersecurity has never been more crucial. AI has the capability to analyze vast amounts of data and identify patterns and anomalies that may indicate potential threats. It has the potential to revolutionize how organizations detect and defend against cyber attacks, offering a proactive approach to cybersecurity.
AI-powered cybersecurity systems can continuously monitor network traffic, user behavior, and system logs to detect any unusual activity. By analyzing historical data and using machine learning algorithms, AI can identify patterns that indicate potential threats. This proactive approach allows organizations to identify and respond to threats before they can cause significant damage. AI can also automate incident response and remediation, reducing the burden on cybersecurity teams and enabling faster response times.
Harnessing AI for Threat Detection and Defense
One of the key areas where AI excels in cybersecurity is threat detection. Traditional rule-based systems are limited in their ability to adapt to new and emerging threats. AI, on the other hand, can learn from past incidents and identify new attack patterns that may not have been previously recognized. Machine learning algorithms enable AI systems to improve their detection capabilities over time, making them increasingly effective in identifying and mitigating cyber threats.
AI-powered threat detection solutions utilize techniques such as anomaly detection, behavioral analytics, and user entity behavior analytics (UEBA) to identify suspicious activity. Anomaly detection involves comparing current behavior against historical data to identify any deviations that may indicate an attack. Behavioral analytics analyze patterns of behavior to identify abnormal actions or deviations from normal behavior. UEBA takes this a step further by using machine learning to establish a baseline of normal behavior for each user and detecting any deviations from that baseline.
Challenges and Limitations of AI in Cybersecurity
While AI brings numerous benefits to cybersecurity, it is not without its challenges and limitations. One of the primary challenges is the constant cat-and-mouse game between attackers and defenders. As AI-powered cybersecurity systems become more sophisticated, hackers also evolve their techniques to bypass detection. Adversarial attacks, where attackers intentionally manipulate data to deceive AI systems, pose a significant challenge in the field of cybersecurity.
Another limitation of AI in cybersecurity is the need for large amounts of high-quality data to train machine learning models effectively. Organizations must ensure they have access to comprehensive and diverse datasets to train AI systems accurately. Additionally, the interpretability of AI models can be a challenge. As AI systems become more complex, it becomes difficult to understand and explain their decision-making process, which may hinder trust and acceptance of these systems.
Despite these challenges and limitations, AI has the potential to greatly enhance cybersecurity efforts. With ongoing research and development, AI-powered cybersecurity systems will continue to evolve and improve, keeping pace with the ever-changing threat landscape.
Sophisticated Threats in Cybersecurity
Overview of Sophisticated Threats
In today’s digital landscape, cyber threats have become increasingly sophisticated. Attackers employ advanced techniques and strategies to exploit vulnerabilities and gain unauthorized access. These sophisticated threats pose significant risks to organizations, their sensitive data, and their reputation. Understanding the nature of these threats is critical in developing effective cybersecurity strategies.
Sophisticated threats encompass a wide range of attack vectors, including malware, phishing, social engineering, insider threats, and more. Attackers often combine multiple techniques and exploit vulnerabilities in various aspects of an organization’s infrastructure. These threats are designed to be stealthy, persistent, and difficult to detect, making them highly dangerous.
Common Techniques Used by Sophisticated Threat Actors
Sophisticated threat actors employ various techniques to carry out their attacks. Some of the common techniques include:
-
Advanced Malware: Attackers create sophisticated malware capable of evading traditional antivirus software. They utilize tactics such as polymorphism, encryption, and obfuscation to make detection challenging.
-
Phishing and Social Engineering: Phishing attacks involve tricking individuals into revealing sensitive information, such as usernames, passwords, or credit card details. Social engineering techniques manipulate human psychology to deceive individuals and gain their trust.
-
Insider Threats: These threats originate from within an organization, often initiated by disgruntled employees or individuals with malicious intentions. Insider threats can result in significant damage, including data breaches, intellectual property theft, and sabotage.
-
Zero-day Exploits: Zero-day exploits take advantage of vulnerabilities that are unknown to the software vendor. Attackers leverage these vulnerabilities to gain unauthorized access to systems or execute malicious code.
-
Advanced Persistent Threats (APTs): APTs are sophisticated, targeted attacks that employ multiple techniques and persistently target specific organizations or individuals over an extended period. These threats often involve a combination of social engineering, malware, and exploit techniques.
Implications of Sophisticated Threats for Organizations
The rise of sophisticated threats has significant implications for organizations across industries. The potential consequences of falling victim to such attacks include:
-
Financial Loss: Sophisticated attacks can result in substantial financial losses due to stolen intellectual property, data breaches, and operational disruptions. Organizations may face legal and regulatory penalties, as well as reputational damage, impacting their bottom line.
-
Data Breaches: Sophisticated attackers target sensitive data, including customer information, proprietary data, and financial records. A data breach can lead to financial fraud, identity theft, and compromised business relationships, eroding customer trust.
-
Disruption of Operations: Cyberattacks can disrupt daily operations, causing significant downtime and productivity loss. Organizations may experience system failures, network outages, and compromised availability of critical services.
-
Reputation Damage: A successful cyberattack can tarnish an organization’s reputation, negatively impacting customer loyalty and brand value. Rebuilding trust and restoring a damaged reputation can be a lengthy and costly process.
To combat these sophisticated threats, organizations must leverage advanced technologies such as AI in their cybersecurity strategies.

AI-Powered Threat Detection
Machine Learning for Anomaly Detection
Anomaly detection is a vital component of threat detection in cybersecurity. AI-powered anomaly detection algorithms have the ability to identify deviations from expected behavior, helping organizations detect and respond to potential threats. Machine learning techniques, such as unsupervised learning, are commonly used for anomaly detection.
AI-based anomaly detection models learn patterns from historical data and establish a baseline of normal behavior. Any deviations from this baseline are flagged as anomalies and may indicate a potential threat. Machine learning algorithms can analyze vast amounts of data and identify anomalies in real-time, providing organizations with valuable insights into potential attacks.
Behavioral Analytics and User Entity Behavior Analytics (UEBA)
Behavioral analytics and user entity behavior analytics (UEBA) are powerful tools in AI-powered threat detection. Behavioral analytics analyze patterns of behavior, such as network activity, user actions, and system logs, to identify suspicious or anomalous behavior. By continuously monitoring user behavior and establishing baselines, AI systems can detect any deviations that may indicate a potential threat.
UEBA takes behavioral analytics a step further by leveraging machine learning algorithms to establish individual baselines for each user or entity. This allows for more granular analysis, as deviations from an individual’s typical behavior can be identified and flagged as potential threats. UEBA is particularly effective in detecting insider threats, as it can identify abnormal activity from authorized users.
Network Traffic Analysis and Intrusion Detection
AI-powered network traffic analysis and intrusion detection systems play a crucial role in detecting and preventing cyber threats. By analyzing network traffic, these systems can identify suspicious connections, potential malware infections, and unauthorized access attempts. AI algorithms can learn from historical network data to identify patterns and anomalies that may indicate threats.
Intrusion detection systems (IDS) leverage AI techniques to monitor network activity and detect potential intrusions. By analyzing network packets, IDS can identify malicious or unauthorized activity, such as port scanning, brute force attacks, or attempts to exploit vulnerabilities. When an intrusion is detected, IDS can trigger alerts or take automated actions to mitigate the threat.
By harnessing the power of AI, organizations can strengthen their threat detection capabilities, enabling them to identify and respond to cyber threats in real-time.
Cyber Defense with AI
Automated Incident Response and Remediation
AI-powered cybersecurity systems offer the ability to automate incident response and remediation processes. In the event of a cyber attack, AI systems can instantly analyze incoming data, identify the nature of the attack, and initiate the appropriate response. This automation reduces the burden on cybersecurity teams, enabling faster response times and minimizing the impact of attacks.
Automated incident response can involve isolating infected systems, blocking malicious IP addresses, or applying patches and updates to vulnerable software. By automating these processes, organizations can respond to incidents promptly, reducing the time it takes to mitigate potential damage.
Cloud Security and AI
As organizations increasingly adopt cloud-based solutions, the importance of cloud security cannot be overstated. AI plays a crucial role in enhancing cloud security by continuously monitoring and analyzing cloud environments. AI algorithms can detect unauthorized access attempts, abnormal behavior, and potential security vulnerabilities within cloud infrastructure.
AI-powered cloud security solutions can automatically identify misconfigurations, unauthorized access, and potential data breaches. By leveraging machine learning and behavioral analytics, AI can provide real-time visibility into cloud environments, enabling organizations to detect and respond to threats effectively.
Adaptive Authentication and Biometrics
AI-powered authentication systems offer enhanced security by providing adaptive authentication and leveraging biometrics. Adaptive authentication analyzes multiple factors, such as user behavior, device information, and location, to determine the level of risk associated with a login attempt. If a login attempt is deemed high risk, additional authentication measures, such as multifactor authentication, can be triggered.
Biometrics, such as fingerprint or facial recognition, provide a more secure form of authentication than traditional passwords. AI can analyze biometric data and compare it against stored templates to verify the identity of users. This reduces the risk of unauthorized access and improves overall security.
By incorporating AI into their cyber defense strategies, organizations can strengthen their security posture, enhance incident response capabilities, and protect their digital assets effectively.

AI in Vulnerability Management
Automated Vulnerability Detection and Prioritization
Vulnerability management is a critical aspect of cybersecurity, as it involves identifying and prioritizing vulnerabilities to mitigate potential risks. AI can play a significant role in this process by utilizing automation and machine learning algorithms.
AI-powered vulnerability management systems can automatically scan networks, systems, and applications to identify potential vulnerabilities. By analyzing historical vulnerability data and security advisories, these systems can prioritize vulnerabilities based on factors such as severity, exploitability, and potential impact. This allows organizations to allocate their resources effectively and address critical vulnerabilities first.
Continuous Monitoring and Scanning
Effective vulnerability management requires continuous monitoring and scanning to stay ahead of emerging threats. AI can enable continuous vulnerability assessment by automating the scanning process and analyzing the results in real-time.
By continuously scanning networks, systems, and applications, AI-powered vulnerability management systems can identify new vulnerabilities as they emerge. Machine learning algorithms can learn from past vulnerabilities and adapt to new patterns, helping organizations stay proactive in their vulnerability management efforts.
Patch Management and Software Updates
AI can streamline the patch management process by automating the identification, testing, and deployment of patches and software updates. By analyzing vulnerability data and software dependencies, AI systems can identify the most critical patches and prioritize their deployment.
Automated patch management reduces the risk of unpatched vulnerabilities, which are often exploited by attackers. AI can also analyze the impact of patches before deployment, minimizing the risk of system downtime or compatibility issues.
By leveraging AI in vulnerability management, organizations can enhance their ability to identify, prioritize, and remediate vulnerabilities, reducing the overall risk to their systems and data.
AI in Phishing and Social Engineering Prevention
Email Filtering and URL Analysis
Phishing attacks continue to be one of the most prevalent cyber threats, targeting individuals and organizations alike. AI can significantly enhance phishing prevention efforts by automating email filtering and analyzing URLs for potential threats.
AI-powered email filtering systems utilize machine learning algorithms to identify and block suspicious emails. These systems can analyze email content, sender reputation, and other factors to determine if an email is likely to be a phishing attempt. By continuously learning from new phishing patterns, AI systems can adapt and improve their detection capabilities over time.
URL analysis is another critical component of phishing prevention. AI can analyze URLs embedded in emails or websites to identify potential malicious links. By comparing the URL against a database of known malicious URLs or using machine learning models, AI systems can identify suspicious URLs and warn users before they access them.
AI-Powered Fraud Detection
Fraud detection is essential for organizations that handle sensitive customer information and financial transactions. AI-powered fraud detection systems can analyze vast amounts of data and identify patterns that may indicate fraudulent activity.
By leveraging machine learning algorithms, AI systems can learn from historical fraud data and detect anomalies in real-time. These systems can identify patterns of suspicious behavior, such as unusual spending patterns, account takeovers, or fraudulent transactions. By continuously learning and adapting, AI-powered fraud detection systems can stay one step ahead of fraudsters.
User Behavior Analytics for Phishing Prevention
User behavior analytics, combined with AI, can be instrumental in phishing prevention. AI systems can analyze user behavior, such as email response patterns, click rates, and download activities, to establish a baseline of normal behavior for each user. Any deviations from this baseline can be flagged as potential indicators of a phishing attempt.
By leveraging AI-powered user behavior analytics, organizations can detect phishing attempts that may bypass traditional email filters. This approach provides an additional layer of protection against sophisticated phishing attacks.
By incorporating AI into their phishing prevention strategies, organizations can better protect themselves and their users from falling victim to these malicious attacks.

AI in Malware Detection and Prevention
Behavior-Based Malware Analysis
AI plays a vital role in malware detection and prevention by using behavior-based analysis. Traditional signature-based antivirus systems are limited in their ability to detect new and emerging malware strains. AI-powered malware detection systems, on the other hand, can analyze the behavior of files and processes to identify potentially malicious activity.
By utilizing machine learning algorithms, AI systems can learn from historical malware data and identify behavioral patterns that may indicate a malware infection. These systems can detect malicious behavior, such as unauthorized file modifications, network connections to known malicious IP addresses, or attempts to exploit vulnerabilities.
Real-Time Threat Intelligence and Machine Learning Models
Real-time threat intelligence and machine learning models are powerful tools in AI-powered malware detection and prevention. Real-time threat intelligence involves continuously monitoring for new malware strains, analyzing their behavior, and updating detection systems in real-time.
Machine learning models can adapt to new and evolving malware threats by incorporating real-time threat intelligence data. By analyzing the behavior of known malware strains and identifying common characteristics, these models can detect new and emerging malware variants.
Endpoint Protection with AI
Endpoint protection is critical in preventing malware infections and protecting individual devices. AI-powered endpoint protection solutions utilize machine learning algorithms to analyze endpoint activity and identify potential threats.
By continuously monitoring endpoints, AI systems can detect suspicious or abnormal behavior, such as unauthorized access attempts, file modifications, or network connections to malicious IP addresses. These systems can proactively block or isolate potentially infected endpoints, preventing the spread of malware within the network.
By leveraging AI in malware detection and prevention, organizations can enhance their ability to detect and mitigate malware threats, reducing the risk of data breaches and system compromises.
AI in Insider Threat Detection
Identifying Anomalous User Behavior
Insider threats pose a significant risk to organizations, as authorized users can exploit their access to carry out malicious activities. AI can play a crucial role in detecting insider threats by analyzing user behavior and identifying anomalies that may indicate potential malicious intent.
AI-powered insider threat detection systems continuously monitor user activity, such as file access, system logins, or data transfers. By establishing a baseline of normal behavior for each user, AI systems can identify any deviations that may indicate suspicious or unauthorized activity. These systems can then trigger alerts or take automated actions to mitigate the threat.
Privileged User Monitoring and Analysis
Privileged users, such as system administrators or senior executives, often have access to sensitive data and critical systems. Monitoring and analyzing the behavior of privileged users are essential in detecting insider threats.
AI systems can analyze the behavior of privileged users, such as their access patterns, file modifications, or network activity, to identify any suspicious or unauthorized actions. By continuously monitoring privileged user behavior and comparing it against established baselines, AI systems can detect any deviations that may indicate potential malicious activities.
Data Loss Prevention (DLP) with AI
Data loss prevention (DLP) is a critical aspect of insider threat detection and prevention. AI-powered DLP systems can automatically analyze and classify sensitive data, such as personally identifiable information (PII) or intellectual property. These systems can monitor data in motion, at rest, and in use to detect unauthorized access or data exfiltration attempts.
By leveraging machine learning algorithms, AI-powered DLP systems can learn from historical data loss incidents and identify patterns associated with potential data breaches. These systems can enforce policies to prevent data loss, such as blocking unauthorized file transfers or alerting administrators of suspicious activities.
By using AI in insider threat detection, organizations can enhance their ability to detect and respond to potential insider threats, reducing the risk of data breaches and other malicious activities.
AI in Network Security
Network Traffic Analysis and Intrusion Detection
Network traffic analysis plays a crucial role in network security by monitoring and analyzing network activity for potential threats. AI-powered network security solutions can analyze network traffic in real-time, identifying suspicious connections, abnormal activities, or potential intrusions.
By continuously monitoring network traffic, AI systems can learn the normal behavior of the network and identify any deviations that may indicate an attack. Machine learning algorithms can analyze network packets, identify malicious activities such as port scanning or denial-of-service attacks, and trigger alerts or automated actions.
Automated Threat Hunting and Penetration Testing
Threat hunting and penetration testing are critical in identifying vulnerabilities and ensuring network security. AI can significantly enhance these processes by automating the identification and analysis of potential threats.
AI-powered threat hunting systems can continuously scan networks, systems, and applications for potential vulnerabilities and threats. By leveraging machine learning algorithms, these systems can analyze network traffic, log data, and other indicators to identify patterns associated with potential attacks.
Similarly, AI-powered penetration testing solutions can automate the process of identifying vulnerabilities and testing the security of a network. By simulating attack scenarios and leveraging machine learning models, these systems can identify weaknesses and recommend mitigation strategies.
Security Information and Event Management (SIEM) with AI
Security Information and Event Management (SIEM) systems aggregate and analyze security event logs from various sources to identify potential threats. AI can enhance SIEM capabilities by analyzing large volumes of data, identifying patterns, and automating the identification of potential threats.
AI-powered SIEM systems can analyze logs, event data, and network traffic to detect security incidents in real-time. By continuously learning from new data and utilizing machine learning algorithms, these systems can adapt to evolving threats and identify emerging attack patterns.
By incorporating AI into network security strategies, organizations can improve their ability to detect and respond to potential threats, ensuring the security of their networks and data.
Future of AI in Cybersecurity
Increasing Sophistication of AI-Powered Cyber Attacks
As AI continues to advance, there is a growing concern about the use of AI in cyber attacks. Sophisticated threat actors are increasingly leveraging AI to develop more sophisticated and targeted attacks. AI-powered attacks can automate tasks such as reconnaissance, evasion, or adapting to changing environments, making them even more challenging to detect and defend against.
To combat AI-powered cyber attacks, organizations will need to adopt AI themselves, harnessing its capabilities to strengthen their defenses. This will require ongoing research and development to stay ahead of emerging threats and continuously improve cybersecurity systems.
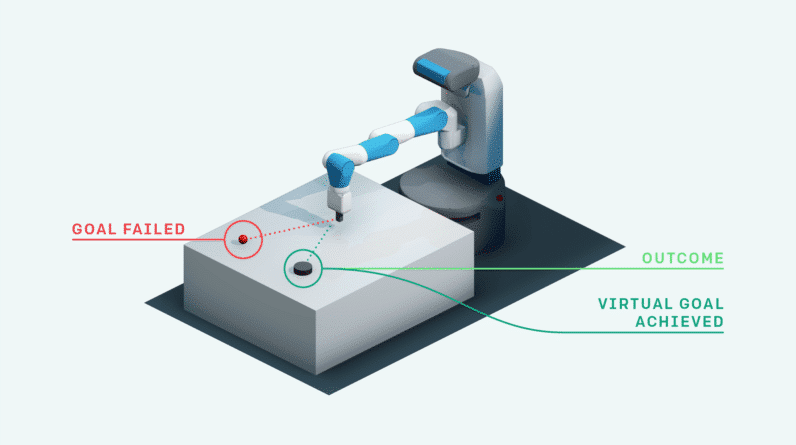
The Role of AI in Autonomous Security Systems
The future of cybersecurity will likely involve the integration of AI into autonomous security systems. These systems will leverage AI to autonomously detect, analyze, and respond to cyber threats without human intervention. By combining AI with automation and orchestration capabilities, organizations can significantly improve their ability to respond to threats in real-time.
Autonomous security systems can continuously monitor and analyze vast amounts of data, detecting anomalies, identifying patterns, and taking appropriate actions to mitigate potential threats. These systems can free up cybersecurity teams from mundane tasks and enable them to focus on strategic initiatives, threat hunting, and incident response.
Ethical Implications and Challenges of AI in Cybersecurity
As AI becomes increasingly prominent in cybersecurity, ethical considerations and challenges emerge. One major concern is the potential for AI systems to be manipulated or compromised by malicious actors. Adversarial attacks can deceive AI systems, leading to false positives or false negatives, undermining the effectiveness of cybersecurity defenses.
Another ethical challenge is the need for transparency and explainability in AI decision-making processes. As AI systems become more complex, it can be difficult for humans to understand and explain how the system arrives at its decisions. This lack of transparency can hinder trust and raise concerns about bias or discrimination in AI models.
Addressing these ethical implications and challenges will require ongoing research, development, and regulation. Organizations must ensure that AI systems are secure, robust, and accountable, and that they align with ethical standards and principles.
In summary, AI has become an essential tool in cybersecurity, offering the potential to detect and defend against increasingly sophisticated threats. From threat detection and defense to vulnerability management, AI-powered solutions can greatly enhance an organization’s cybersecurity posture. While challenges and ethical considerations exist, the future of AI in cybersecurity holds great promise for organizations looking to protect their digital assets and ensure the privacy and security of their customers.